Our Solution
SecureKloud is constantly monitoring the client's AWS resources and AWS Network Security using various tools as we are already engaged with the client as their AWS Managed Services partner.
After analysing client's existing Network Security Setup, SecureKloud proposed the following solution to protect their data from unauthorized access.
Based on the research on the DDoS attacks due to different requirements from different clients, SecureKloud has developed solutions that include customization and implementation of third-party tools such as Cloudflare and Imperva. This is done to mitigate DDoS protections for the applications running in the Client AWS accounts.
SecureKloud customized and implemented the Cloudflare tool as per the client's requirements to provide DDoS protection for their critical applications.
As a part of its Cloud DevOps for Innovation and Maturation (CDIM) approach, SecureKloud constantly keep updating the Cloudflare configuration based on the updates in their critical applications to ensure complete protection from DDoS attacks
Cloudflare protects and accelerates all websites, apps, and APIs with unmetered DDoS protection, a global CDN, and more.
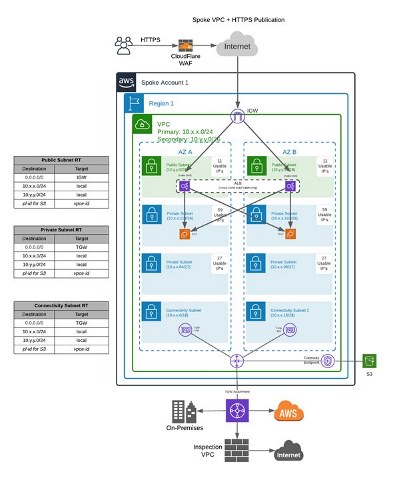
To secure the service, all inbound traffic passes through a cloud-based Cloudflare Web Application Firewall (WAF). The WAF routes traffic to the ALB, via DNS name resolution, where it is then load-balanced to the backend instances.
All public facing applications should be configured to route the traffic via DMZ Zone. So, the Internet traffic will first hit the External Load balancer of the DMZ Account in AWS. Then the traffic will be routed to the backend host of Cloudflare instance where web filtering happens and then the Cloudflare directs the traffic to the Client's internal Load balancer. Similarly, the reverse traffic is routed back to the internet via Imperva Revers proxy.
To prevent direct access from the internet to the front end of the ALB a security group has to be added to the ALB with an inbound rule allowing only the IP ranges of Cloudflare. Those ranges can be found on Cloudflare's public website (https://www.cloudflare.com/ips/). By default, only port 443 is allowed inbound by the security group from the Cloudflare public IPs.